Cyber Threat Activities from the Russia-Ukraine Cyberwar
The Russian incursion into Ukraine has led to a conflict that involves both the physical and cyber domains, with hacking groups of differing allegiances launching cyberattacks on government, military, financial and telecommunication websites. Cybersecurity specialists worldwide have highlighted growing concerns that the intensifying conflict between Russia and Ukraine may spillover in the form of cyberattacks launched at governments and companies on a global scale.
From the onset of the Russia-Ukraine conflict in 2014, Ukraine has been subjected to a series of high-profile cyberattacks on its national infrastructure, industries, and government websites. These attacks, which have long been suspected to have Russian involvement, have escalated to over 150 incidents in the lead-up and ongoing military operations in Ukraine.
A large concentration of notable cyberattacks that have recently targeted Ukraine involve:
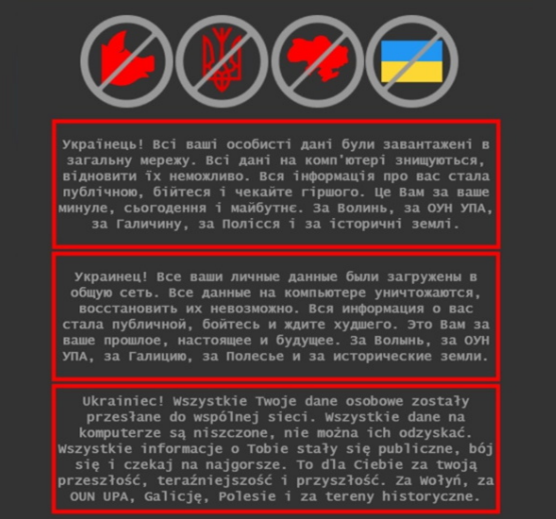
- Web defacements on at least 70 government websites, including the exploitation of outdated Content Management Systems (CMS).
- Distributed Denial of Service (DDoS) on Ukrainian financial institutes and government websites.
- Destructive Wiper malware that corrupts the Master Boot Record (MBR) of system hard drives and rendering them unbootable.
- Decoy ransomware being deployed alongside wiper malware to confuse and divert incident response teams away from the real damage being inflicted from the latter.
The nature of employing multiple Tactics, Techniques and Procedures (TTPs) against Ukraine, bear strong semblance to the cyberwarfare doctrine employed by Russian state-sponsored threat actors. In a public webcast on the ‘Russian Cyber Attack Escalation in Ukraine’ on 25 February 2022, security experts from the SANS Institute assessed that Russian government operators are primarily focused on targeting their Ukrainian state-level counterparts . Furthermore, the potential for a Russian retaliatory cyberattack on non-Ukrainian entities include a balance of the following considerations:
- Targets that can result in disruption, and undermine public sentiments against Russia
- Will not be seen as act of war by the country in which the Victim resides
- Does not exhaust valuable attack vectors that are suited for cyberconflicts of a higher severity (i.e., use common and easily reproduceable attack methods such as DDoS to convey a limited ‘show of force’)
- Will not limit future intelligence collection against the target (retaining the potential for future reconnaissance and Advance Persistent Threat deployment)
- Is not a target Russia will want to impact if diplomatic sanctions with US/EU escalate.
In addition to these factors, the Kremlin officially approved a list of ‘unfriendly’ countries and territories on 7 March 2022 that that included but were not limited to the United States, European Union nations, as well as Singapore, Japan, and Australia . Therefore, website owners worldwide are strongly advised to assess whether their organisations fall within this attack scope, in order to carry out the necessary risk mitigations and reinforce their security posture.
Another concerning observation is the growing involvement of hacktivist organisations on both sides of the Russia-Ukraine conflict, who unlike their state-equivalents, have greater autonomy to attack overseas targets and further their respective state’s agenda under the guise of anonymity with minimal ramifications. Hacker groups such as Anonymous and Free Civilian have conducted their own operations by performing DDoS attacks on Russian websites and claimed to have sold compromised Ukrainian citizen data respectively. Consequently, hacktivist groups may extend these malicious activities worldwide by the indiscriminate targeting of entities and their websites worldwide.
Large scale cyberattacks in the past, particularly those that involved the transmission of malware, have been known to affect entities beyond their intended target(s). A notable example of this was the spread of a Russian-originated ransomware called NotPetya, which targeted Ukrainian banks, airports and powerplants on 27 June 2017, but quickly propagated worldwide to affect government agencies, corporations, and maritime shipping. According to the U.S Homeland Security Advisory Tim Bossert, the aftermath of the NotPetya malware was a purported sum of $10 billion in financial damages globally .
In response to the growing spill-over risk of global cyberattacks from Eastern Europe , government bodies such as the Singaporean Cybersecurity Agency (CSA) have issued an advisory calling for local firms to strengthen their security posture against attacks such as web defacement, distributed denial of service (DDoS), and ransomware.
The most common attack surface that has been subjected to all three of these methods is an organisation’s website on the internet. Consequently, any organisation that is reachable via their website is susceptible to a cyberattack if not secured properly, which can lead to irreparable reputation loss, financial damage, regulatory penalties. “Given the very high tensions that we are experiencing, companies of any size and of all sizes would be foolish not to be preparing right now as we speak to increase their defences, to do things like patching, to heighten their alert, to be monitoring in real time, their cybersecurity,” said Deputy Attorney General Lisa Monaco during the Munich Security Conference .

If you currently own a website or are taking care of a web application, a strengthened cyber posture is highly recommended to counter the potential effects of collateral damage (e.g., DDoS, defacements, ransomware) from the Russia-Ukraine war.
DDoS attack prevalence has risen considerably over the past few years. According to Cloudflare in Q4 2021, random DDoS attacks have increased by 29% year-on-year . In December 2021 alone, websites faced more DDoS-type attacks than the quantities reported for Q1 and Q2 of the same year. Organisations can adopt several DDoS mitigation strategies to protect their websites. These include implementing effective network monitors to detect such DDoS attacks, setting traffic thresholds to limit the number of HTTP requests, as well as ensuring sufficient network bandwidth and server capacity to withstand occasional traffic spikes . Additional measures include enlisting cloud-based services and a Content Delivery Network (CDN) to host and support web servers, where the benefits of scalability, wider bandwidth and diversity of security services can guard websites from DDoS attacks.
Web defacements are another common threat for organisations, where a malicious agent seizes control of a website and replaces the original content with their own page. The general intent of web defacements is to tarnish the reputation of the targeted organisation, or to convey the malicious party’s message to the site’s visitors. Government sites and businesses are especially vulnerable, for a successful defacement can lead to a loss in public confidence. Safeguards against web defacements include limiting administrator access, and reducing the attack surface and potential for zero-day vulnerabilities by being selective about the of web application plugins usage . Advanced methods of web defacement prevention include periodic scans for unauthorised changes and vulnerabilities on web applications, as well as input sanitisation via a web application firewall to prevent SQL injections and Cross Site Scripting (XSS).
Ransomware attacks saw an unprecedented growth in 2021 that affected both industrial and information systems alike. According to a report by the International Data Corporation (IDC), approximately 37% of global organisations were victims of ransomware attacks in 2021 . Global agencies such as the European Union Agency for Cybersecurity (ENISA) reported a 150 percent rise in ransomware attacks in 2021, warning that the trend will likely continue in 2022. Ransomware victims are increasingly being faced with a ‘triple-threat strategy,’ from their attackers, who threaten to a) publicly release stolen confidential information; b) disrupt the victim’s core functionality such as internet access; and c) directly harm the victim’s reputation by broadcasting the data breach to customers, shareholders, and the public . Ransomware is commonly propagated through unsafe links embedded in email phishing campaigns, but may also be inserted through other vectors such as USBs and file uploads. Therefore, common preventative measures to counter ransomware attacks include file integrity monitoring software, firewalls to filter and block malware traffic as well web server backups and storing them offline .

Implementing a stack of security tools to face the cyberattacks mentioned and staffing a team to handle such threats can be a major challenge for organisations, given the complexities of attacks and an ever-present talent shortage. The WebOrion® Suite is Cloudsine’s answer to many of these concerns, providing a comprehensive security package that includes a fine-tuned Web-Application Firewall, Website Monitor and Restorer, enabling system operations teams to better prevent, detect and remediate cyberattacks.
The versatility of the WebOrion® Monitor and Restorer VX2 Virtual Appliances allows for them to be deployed in a diverse range of on-premises and cloud environments. Website owners looking for a seamless integration can adopt the WebOrion® Cloud, an all-inclusive Software-as-a-Service (SaaS) platform that is designed to be highly modular, and scalable to counter the latest web security challenges.
If you are interested to learn more about how the WebOrion Suite can help you with your website’s protection, do contact us via our Contact Us Page.
For more information on how WebOrion can act as a countermeasure to web attacks and more, access our curated White Papers via the WebOrion Website.
Reference links:
- https://www.dw.com/en/ukraine-cyberwar-creates-chaos-it-wont-win-the-war/a-60999197
- https://www.sans.org/webcasts/russian-cyber-attack-escalation-in-ukraine/
- https://tass.com/politics/1418197?utm_source=google.com&utm_medium=organic&utm_campaign=google.com&utm_referrer=google.com
- https://www.industrialcybersecuritypulse.com/throwback-attack-the-notpetya-malware-causes-serious-damage-to-snack-giant-mondelez/
- https://www.fitchratings.com/research/structured-finance/russia-ukraine-war-increases-spillover-risks-of-global-cyberattacks-04-03-2022
- https://www.defenseone.com/technology/2022/02/us-companies-warned-prepare-russian-cyber-attacks/362172/
- https://blog.cloudflare.com/ddos-attack-trends-for-2021-q4/
- https://www.cdnetworks.com/cloud-security-blog/tips-to-protect-your-business-from-ddos-attacks/
- https://www.imperva.com/learn/application-security/website-defacement-attack/
- https://www.idc.com/getdoc.jsp?containerId=prUS48159121
- https://www.arcserve.com/nsa-fbi-and-cisa-issue-global-ransomware-threat-advisory
- https://industrywired.com/7-pro-tips-to-protect-your-website-from-ransomware-attacks/
Authored by Toby Lim, Associate Security Consultant
Edited By Cloudsine – WebOrion Security Team

