CloudGoat is a “Vulnerable by Design” AWS deployment tool built by Rhino Security Labs, an US-based penetration testing company.
(Github Link)
It has several “Capture-The-Flag” based scenarios baked into it and each scenario contains a vulnerable set of AWS resources designed for users to hone their cloud cybersecurity skills.
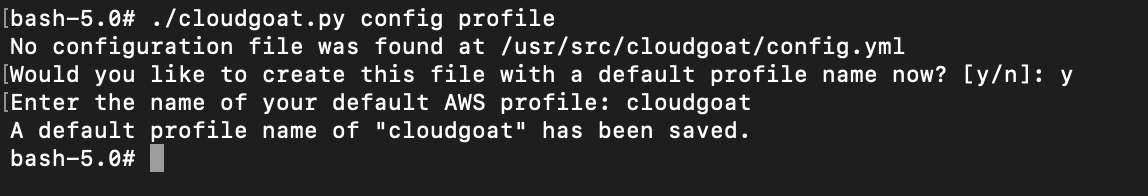
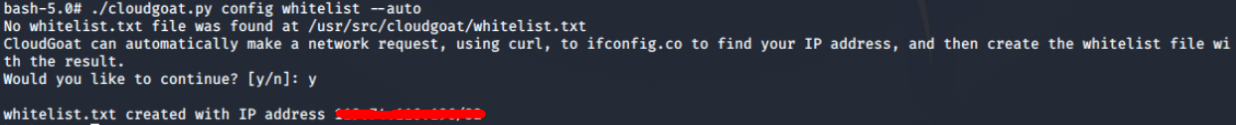
CloudGoat also uses a deployment script (Using Terraform) that allows users to deploy/shutdown the entire cloud environment programatically and automatically.
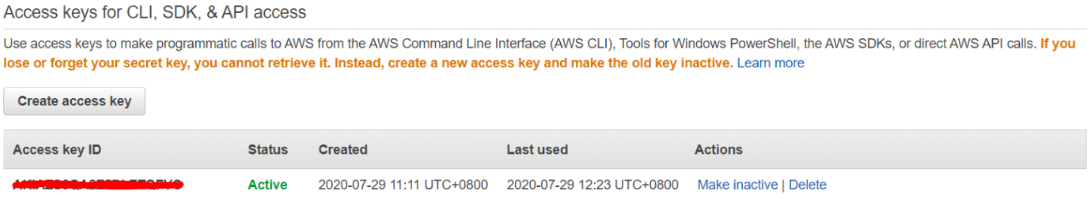
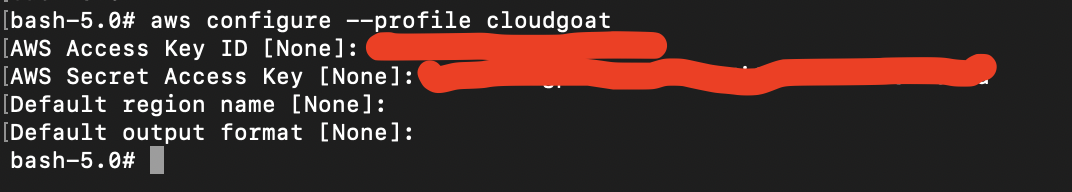
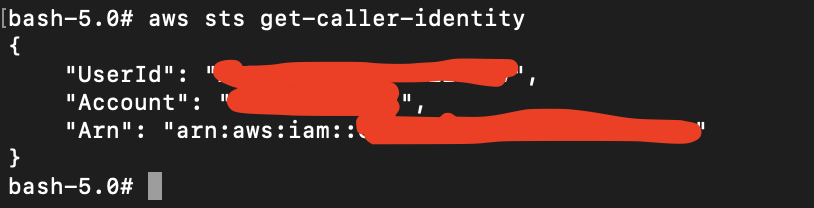
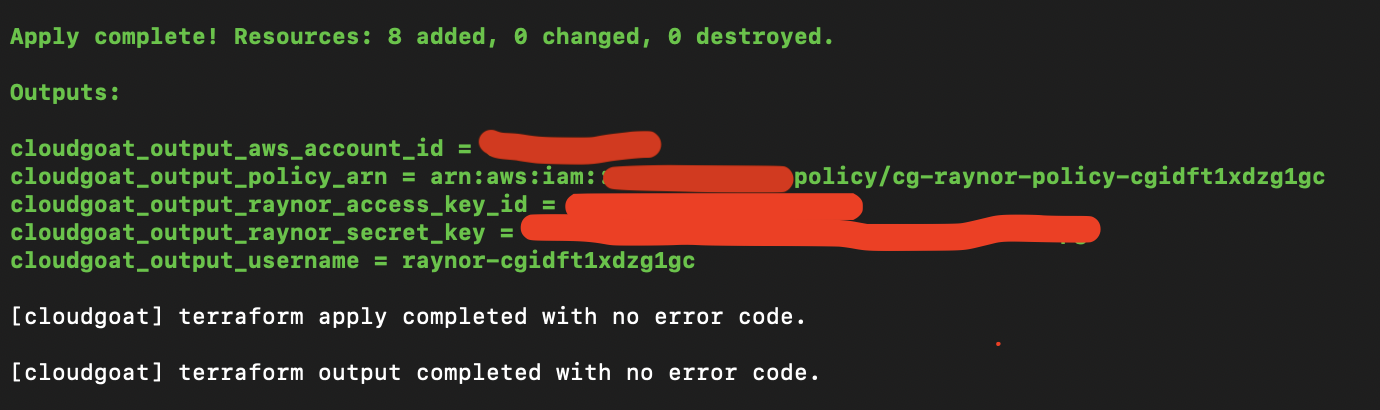
It will generate passwords and key pairs that are used within the environment and output them to a file in the CloudGoat working directory.
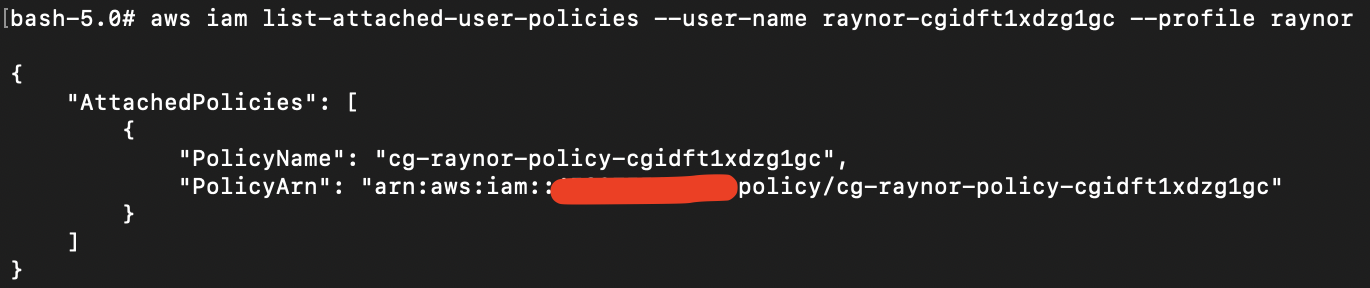
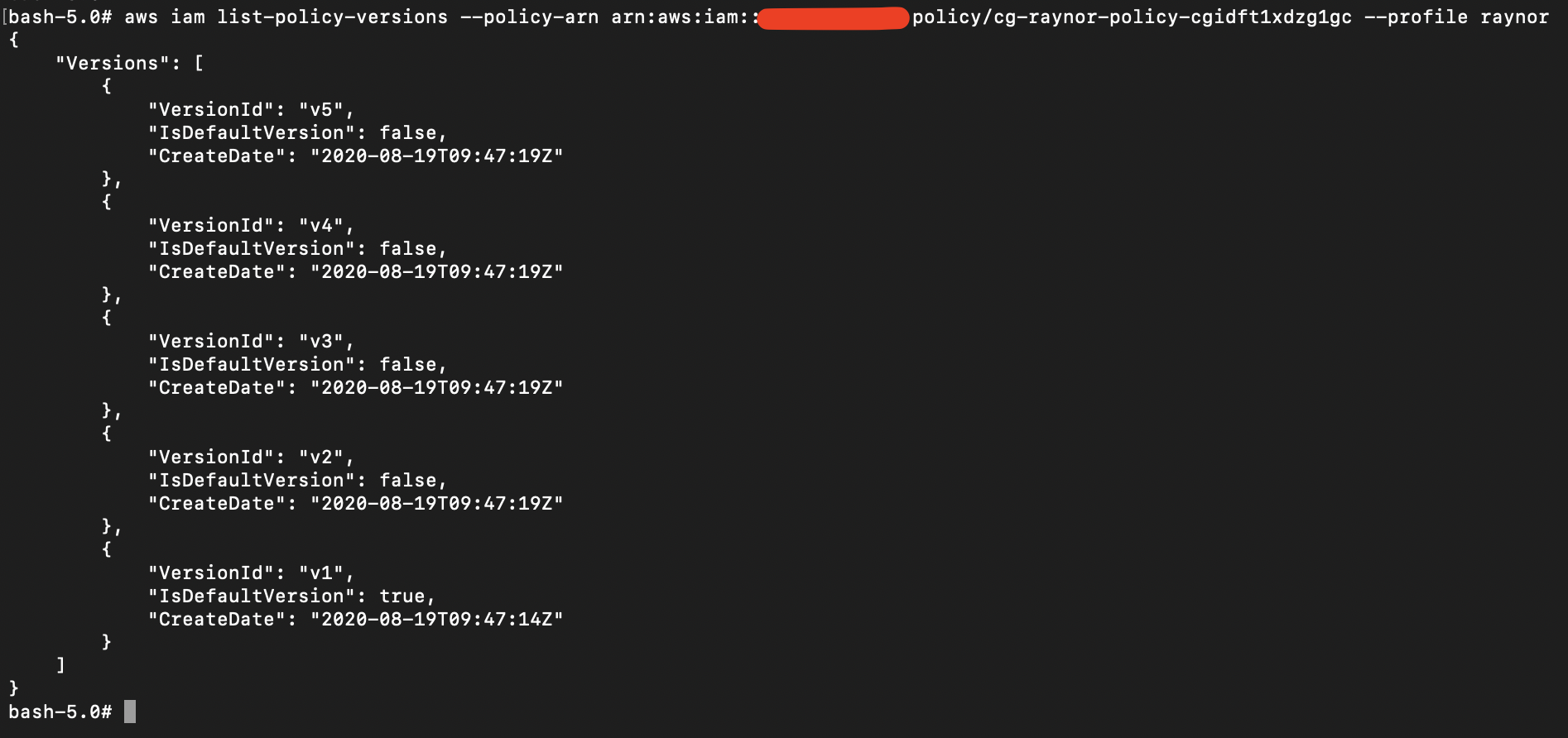
These credentials stand as a starting place when attacking the environment.
Each scenario is composed of AWS resources arranged together to create a structured learning experience. There are a total of seven scenarios and these scenarios have different ranges of difficulties, and most of the scenarios’ vulnerabilities are caused by privilege escalation.
You can launch it into your AWS account and leave it running, without having to worry about external threats (Security Groups and settings will be automatically set to only allow your IP address). However, we advise that you do NOT run this in your actual account but on a testing/throwaway account instead.
Due to the length of the content, we will be splitting up the Scenarios into various parts. This current article will be about Scenario 1, and thereafter will be Part 2 (Scenario 2&3), Part 3 (Scenarios 4&5), Part 4 (Scenario 6) & Part 5 (Scenario 7). We have arranged the difficulty of the scenarios in ascending order. The main aim here is to break down each step so that it is easy to understand the underlying motivations.
Most of the scenarios involve you to perform privilege escalation, so it is important to understand what it does, and how it works.
Before we start, there are 2 ways of running CloudGoat. Click on each link to see how to run:
- Docker
- Manual Installation